Understanding the Value of Ensemble of Moving Target Defenses in Morpheus
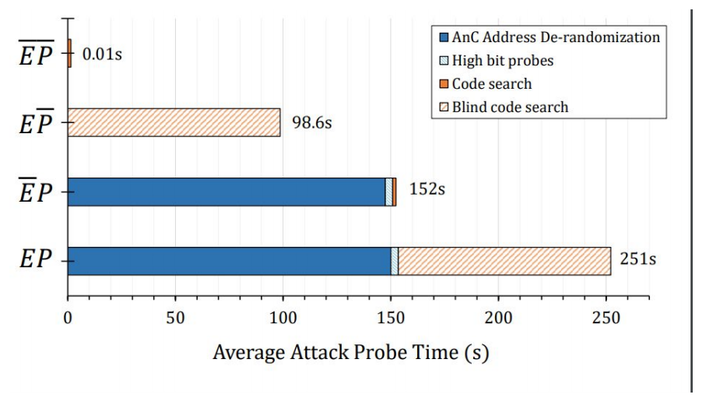 Time to penetrate a de-featured Morpheus
Time to penetrate a de-featured Morpheus
In this work, I studied the average time needed to penetrate a de-featured Morpheus design. The result underscores the robustness of Morpheus defenses.